Application of Quantum Simulator and QLLM Based on BSM-SG for Q-SIEM
1. Introduction
Quantum Security Information and Event Management (Q-SIEM) systems represent a new generation of platforms that leverage quantum algorithms and machine learning for threat detection. Traditional SIEM (Security Information and Event Management) systems suffer from issues such as:
- Latency in analyzing large log volumes
- False positives and negatives in attack analysis
- Limited event correlation capabilities
- Lack of adaptability to new threats
BSM-SG Q-SIEM combines BSM-SG theory with quantum simulations and a self-learning quantum language model (QLLM) to enhance incident detection and response.
2. How the System Works
The system consists of three main components:
2.1. Quantum Simulator for Atomic Structures (BSM-SG Quantum Simulator)
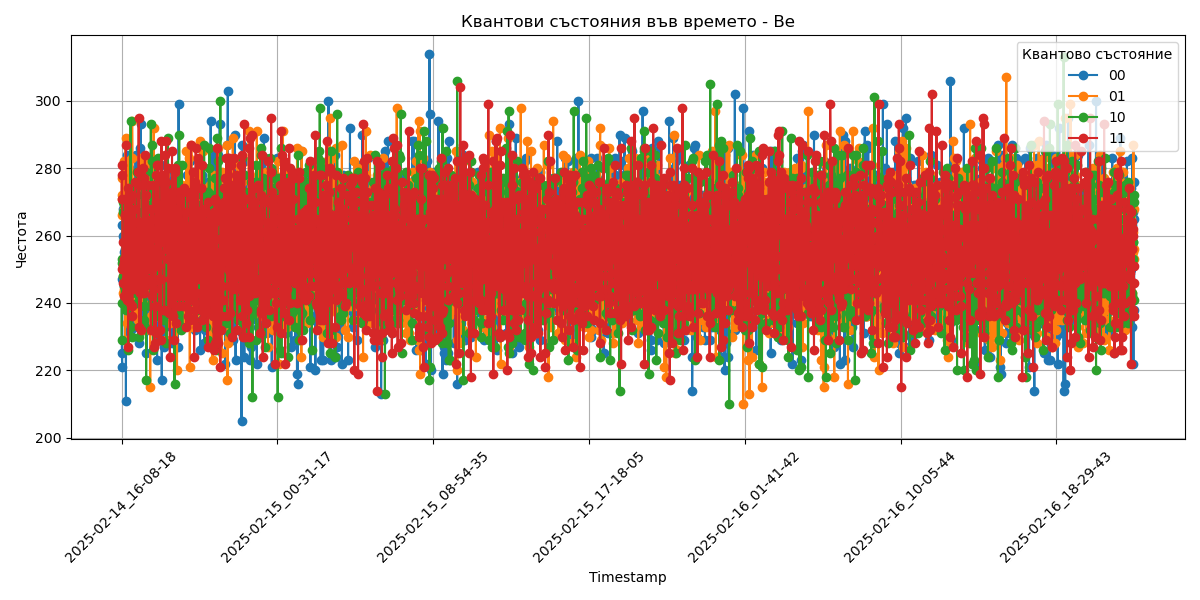
Quantum simulation of elements such as Beryllium (Be) and Strontium (Sr) is based on:
- The spin states of electrons and neutrons according to BSM-SG
- Interactions between orbital electrons and nuclear configurations
- Stability of various quantum states
Through this simulation, we analyze the stability of quantum bits (qubits) using an algorithm that models the rotation and oscillation of subatomic particles within the atomic lattice structure.
2.2. QLLM (Quantum Large Language Model)
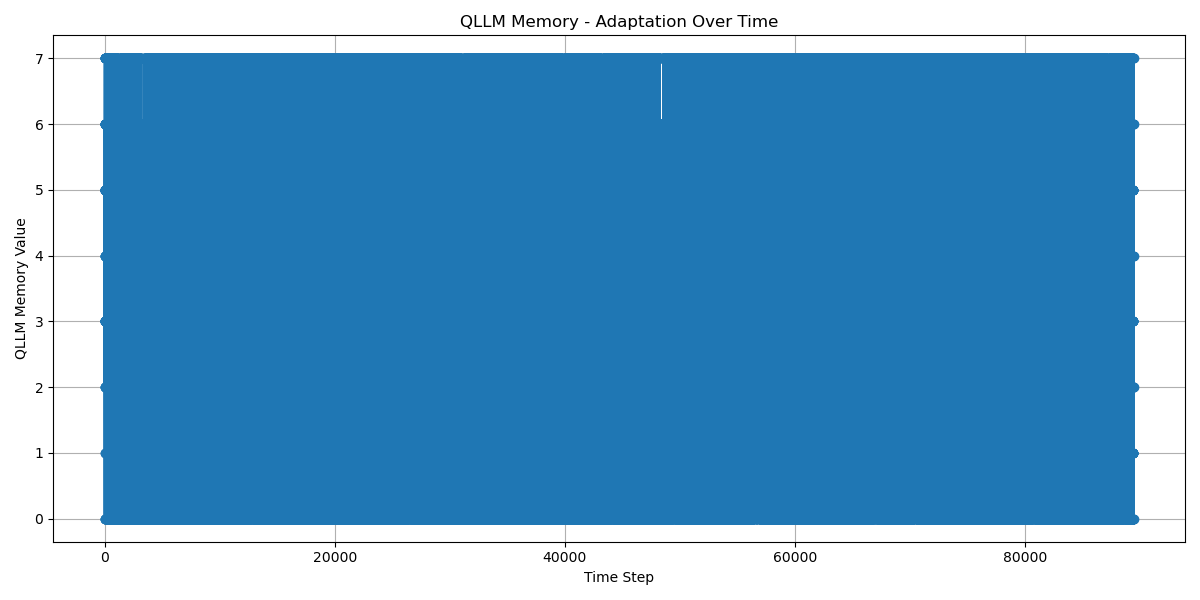
QLLM is a self-learning neural network that:
- Learns the probabilistic distribution of quantum states
- Adapts quantum gates for optimal performance
- Trains on logs from the SIEM system
- Automatically detects anomalies and emerging threats
In this model, QLLM vectorizes quantum states by applying wave functions based on BSM-SG theory to identify anomalies and hidden patterns.
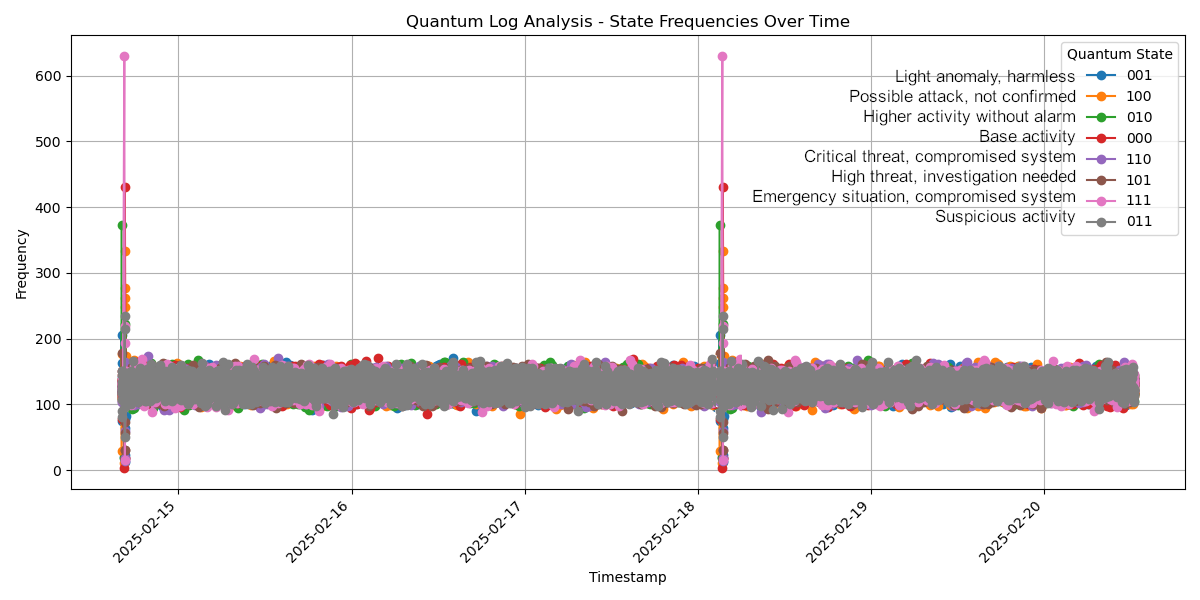
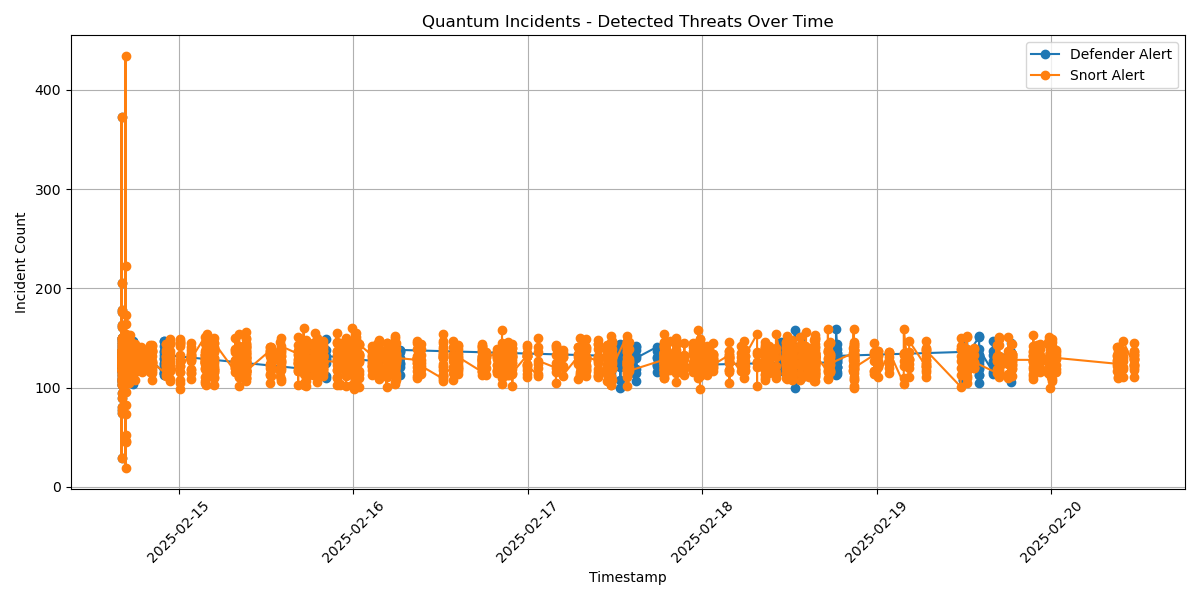
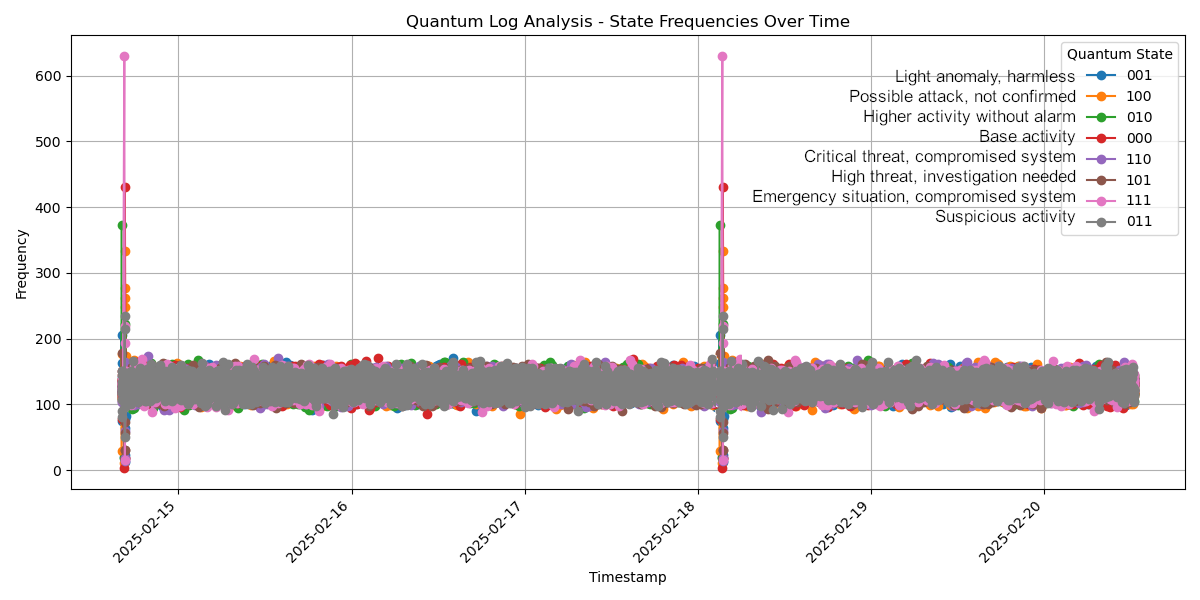
2.3. Integration with Q-SIEM
BSM-SG Q-SIEM receives logs from SIEM systems (Graylog, Snort, Defender), vectorizes them, and analyzes them through quantum models. The analysis includes:
- Differentiating logs from various sources (Snort, Defender)
- Determining incident severity through quantum frequency analysis
- Storing incidents in a database
- Sending alerts for critical threats
3. Quantum Analysis Architecture Based on BSM-SG
The key steps in the algorithm are:
- Generating a quantum circuit based on the element (Be, Sr, Mg)
- Applying quantum gates based on BSM-SG:
- X gate (changes the electron spin)
- H gate (quantum superposition)
- CX gate (entanglement between electron and neutron)
- Running the simulation on a quantum backend (AerSimulator)
- Analyzing quantum states using QLLM
- Storing results in a database and performing incident analysis
- Adapting quantum circuits based on input logs (self-learning)
4. Advantages Over Classical SIEM Systems
| Factor | Classical SIEM | BSM-SG Q-SIEM |
|---|---|---|
| Log Analysis | Statistical, ML | Quantum-correlation analysis |
| False Positives | High rate | Dynamic adaptation with QLLM |
| Processing Speed | Linear analysis | Parallel quantum processing |
| Threat Response | Rule-based | Self-learning system |
| New Threats | Difficult to detect | Instant detection via quantum wave functions |
| Scalability | Limited | Theoretically unlimited |
5. Conclusion
BSM-SG Q-SIEM is a revolutionary approach to security, utilizing quantum algorithms inspired by BSM-SG theory to analyze logs and detect incidents. By combining quantum simulations with QLLM, we create an autonomous, self-learning, and highly accurate cybersecurity system.
🚀 Deployments: The system is already fully integrated with production SIEM systems and and is protecting against real-world cyber threats.
2025 Victor Pronchev